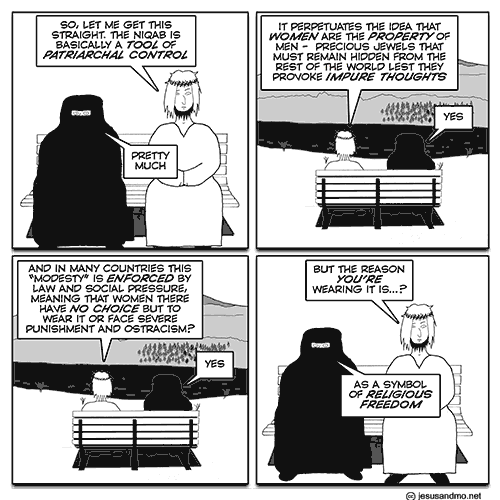
tool
January 25th, 2017
Where on earth did he get that idea from?
Jesus & Mo is licensed under a Creative Commons License:
Feel free to copy for noncommercial purposes, under the same license.
Please provide a link back to jesusandmo.net
Hosted by the amazing NearlyFreeSpeech.NET
Protected by the mighty CloudFlare


Type in third panel: “their” instead of “there”.
Another brilliant strip from Author! Typo in frame 3 – “their” should be “there”. Sorry to be such a pedant!
I note Author’s correction to frame 3. Gee, that was quick!
The religious freedom to make women wear that, amongst many other things. Like the Pilgrims that came to America for the freedom to make everyone amongst them cleave to their religion.
Orwell was off by 33 years.
Excellent, once again, author. You may be interested to know that when I tried to see last week’s cartoon, whilst wandering around Sheikh Zayed Grand Mosque in Abu Dhabi, the screen told me your site was blocked. I am curious to know what other sites are unavailable in Abu Dhabi? I trust the nasty beheading ones are out of reach too?
Spot on as usual. Thank you.
[…] comment is needed on today’s Jesus and Mo strip, expressing the hypocrisy of extolling such a garment as a symbol of either religious freedom or […]
Actually, the much maligned niqab
Is the clothing of a slob
The wearer can drool
Or chew like a mule
Some times, disguised,even a bank, rob.
“Freedom for me but not for thee.” –Anon*
*Nat Hentoff said something different.
I do hope that Mo isn’t wearing a trendy red niqab; I’d hate to see somebody trying to post a letter into his face.
“Freedom’s just another word for nothin’ left to lose . . . .”
“There is always a choice.”
“You mean I could choose certain death?”
“A choice nevertheless, or perhaps an alternative. You see I believe in freedom. Not many people do, although they will of course protest otherwise. And no practical definition of freedom would be complete without the freedom to take the consequences. Indeed, it is the freedom upon which all the others are based.”
(From Terry Pratchett’s “Going Postal”, and perhaps more relevant than ever.)
“[…]If there is a God, it has to be a man.
No woman could or would ever fuck things up like this. So, if there is a God, I think most reasonable people might agree that he’s at least incompetent, and maybe, just maybe, doesn’t give a shit.
Doesn’t give a shit, which I admire in a person, and which would explain a lot of these bad results.”
– George Carlin.
Well done, Author.
This is a sore subject of mine. I can’t help getting kind of furious every time I see someone defending the use of the Hijab in the name of “religious freedom” or cynically using the “women’s choice (to wear what they want)” argument, while at the same time they know that wearing the Hijab in Islam is NOT A CHOICE but an OBLIGATION.
Some of them even say it’s “liberating” (I have to admit this particular argument is hilarious), since Western women are objectified… I can grant that Western women are often regarded as mere sexual objects, but I don’t think that forcing your wife to cover from head to toe and demanding her to satisfy you at any time and not to show her body to anybody else is any different than objectifying her… The Hijab makes women become the property of their husbands.
Thank you for the strip! It’s brilliant!
You all know the theme tune of The Fresh Prince of Bel Air, I assume?
Courtesy of my daughter:
Now this is a story all about how
The world got flipped-turned upside down
And I’d like to take a minute
Just sit right there
I’ll tell you all about the prick with the ridiculous hair
I was to a billionaire, born and raised
In the bankruptcy courts I spent most of my days
Chillin’ out maxin’ relaxin’, a fool
And all groping some pussy outside of the school
With a couple of guys who were wearing the hood
I started blaming latins in your neighborhood
I dissed this disabled guy, but nobody cared
They said, “He’s movin on the White House, but we’re still not scared.”
I whistled for a limo and when it came near
The license plate said “Trump” and it had gold in the mirror
If anything I could say this ride was fine
But I thought, “I’ve got billions”
– “I’m elite, it’s all mine.”
I pulled up to the White House at 7 or 8
And I yelled at the driver, “Go home, migrant labor.”
I looked at my kingdom
With the world in despair
To sit on my throne as the Prick with the hair
Acolyte, thanks for that ear worm. Ah, poetry, eh. I didn’t know you had that talent.
I’m both smiling and seething at that. Good one.
You’ve done it, Acolyte of Sagan. You just nabbed the crown of the poet laureate of the Cock and Bull from Nassar. Good one! Cheers! ^_^
(Also, “The Prick with the Hair” deserves to take its place next to “Orange Hitler”, “Donald Strump” and “Donald Joffrey Trump” as his official epithets.)
Thanks all, but I cannot take the credit, that one was courtesy of my eldest daughter.
Another Trump nickname; Humpty Trumpty.
AoS and talented daughter: Superb, made my day.
Nicknames: The Trumpster
Poster: Large Garbage Bin with Trump’s face on it & the Statue of Liberty partly visible inside.
Slogan: Help get America out of the Trumpster
Jim Baerg, you should create the meme and send it out into cyberspace. I’ll bet it would go viral.
@ Free Fox:
First, and, hopefully, last, EVER, of his name.
to welcome the coming inaugural
a big steaming pile of my doggerel
for the donald to eat
as he suffers defeat.
if not, it’s bound to be bugger all
with the worst of my verses redacted
and the donald’s ascendance enacted
we know in our guts
no if and or buts
we’ll all be severely impacted